Ghost Employee Fraud: Prevention, Detection, and Eradication
TL;DR
Payroll fraud is a silent financial drain. Ghost employee fraud occurs when fictitious, inactive, or deceased individuals are kept on a company’s payroll, draining corporate finances over an average of 18 to 30 months. Highly sophisticated networks, including nation-state remote actors, exploit weaknesses in digital onboarding and identity verification. Organizations must aggressively counter this threat using mathematical forensic auditing, AI-driven anomaly detection, strict segregation of duties, and built-in HCM platform controls like TimeTrex's biometric verification to protect their bottom line and remain compliant.
Article Index
- The Macroeconomic Impact and Taxonomy of Occupational Payroll Fraud
- Structural Mechanics and the Typology of Ghost Employment
- The Insider Threat Matrix and Control Vulnerabilities
- Forensic Diagnostic Indicators and Master File Anomalies
- The Threat of Remote Work and the Digital Phantom
- Mathematical Forensic Auditing and Benford's Law
- Artificial Intelligence and Predictive Analytics in Payroll Ecosystems
- Technological Countermeasures and HCM Software Architectures
- Internal Response Protocols, Legal Liabilities, and Tax Rectification
- Empirical Case Studies in Ghost Payroll Fraud
- Conclusion
The Macroeconomic Impact and Taxonomy of Occupational Payroll Fraud
Occupational fraud constitutes a systemic and pervasive threat to global corporate finance, representing deliberate deception executed by employees or executives for personal financial gain at the direct expense of the organizational entity. Within the broader taxonomy of occupational fraud, asset misappropriation is the most common archetype, and payroll fraud stands as one of its most insidious, costly, and financially damaging subcategories. Ghost employee fraud, a highly structured and premeditated form of payroll theft, occurs when fictitious, inactive, or deceased personnel are deliberately maintained or inserted onto a company’s payroll ledger, allowing a perpetrator to siphon unauthorized wages, benefits, and tax remittances.
The macroeconomic and microeconomic impacts of these fraudulent disbursements are staggering, threatening the solvency of small enterprises and eroding the profit margins of multinational conglomerates. According to comprehensive data aggregated by the Association of Certified Fraud Examiners (ACFE), organizations globally lose an estimated 5% of their total annual revenue to various forms of occupational fraud. Specific statistical models analyzing the period from January 2022 through September 2023 reveal that payroll fraud accounts for approximately 10% to 15% of all investigated occupational fraud cases in the United States and Canada. On a broader international scale, the cumulative devastation is profound; in the United Kingdom alone, annual corporate losses attributed directly to payroll fraud are estimated at a staggering £17 billion.
Because ghost employee schemes are typically perpetrated by trusted insiders possessing systemic administrative access, they inherently bypass superficial audits and traditional financial overviews. Consequently, these schemes operate undetected for an average duration ranging from 18 to 30 months, inflicting median losses that range from nearly $50,000 for small-to-medium enterprises up to an average of $383,000 per incident across broader corporate landscapes, and exceeding $1.5 million in large enterprise schemes. Financial analytics demonstrate that an undetected ghost employee drains approximately $2,800 to $4,000 per month from the victimized organization, according to specialized risk analysis by Moore Colson.
Cumulative Cost Projection (5 Ghost Employees at $4k/mo)
The financial impact of ghost employees compounds aggressively. A small cluster of undetected fictitious records can severely impact operational budgets over a single fiscal year.
Beyond the direct and immediate theft of liquid assets, ghost employee fraud generates a severe cascade of second-order financial and legal liabilities. These encompass artificially inflated payroll tax burdens, heavily distorted labor cost analytics, inaccurate departmental budgeting, and severe regulatory and legal exposure stemming from the submission of falsified financial reporting to federal and state government entities. Furthermore, the reputational damage associated with publicized payroll fraud can deter prospective clients, erode investor confidence, and poison the organizational culture by demonstrating a weak "tone at the top" and severely deficient internal governance. To neutralize this compounding threat, modern enterprises must adopt a multidisciplinary defensive posture that intricately weaves rigorous forensic accounting, advanced predictive analytics, biometric access controls, and strict legal compliance frameworks.
Structural Mechanics and the Typology of Ghost Employment
The conceptual premise of a ghost employee is straightforward, but the logistical execution requires methodical, sustained manipulation of internal corporate systems. A ghost employee is fundamentally defined as an entity residing on the payroll master file that provides absolutely no services, contributes no tangible value to the organization, and exists solely as a financial conduit for embezzlement.
The operational lifecycle of a ghost payroll scheme relies on the continuous execution of four requisite phases. First, the ghost must be successfully added to the organizational payroll database, bypassing human resources verification protocols. Second, the perpetrator must falsify and submit timekeeping data, attendance records, and wage rate authorizations to simulate legitimate labor. Third, the systemic architecture must generate and issue a payroll disbursement, either via a physical paper check or an automated direct deposit file. Finally, the perpetrator or a colluding external accomplice must successfully intercept and convert those funds into untraceable liquid cash.
Typologies of the Phantom Workforce
Ghost employees generally fall into three distinct typologies, each presenting unique forensic challenges and requiring varied methodologies for detection:
The first typology is the completely fictitious identity. In this scenario, the fraudster engineers a synthetic persona from inception. This complex maneuver requires the perpetrator to generate or steal personally identifiable information, such as Social Security Numbers (SSNs), residential addresses, and banking details, to seamlessly bypass human resources onboarding protocols. If the criminal lacks direct access to the overarching Human Resources Information System (HRIS), they are forced to forge onboarding documents, I-9 forms, and direct deposit authorization mandates to create the fictitious account.
The second typology relies on the exploitation of the "zombie record," which involves manipulating the profile of a former or terminated employee. The perpetrator identifies an accidental or deliberate failure by management to remove a terminated, retired, or deceased employee from the active master payroll file. Instead of finalizing the termination protocol and closing the financial record, the perpetrator silently reroutes the outgoing direct deposit routing numbers to an alternative bank account firmly under their control, or intercepts the physical paycheck before it is mailed. This method is highly favored as the employee already possesses a legitimate digital footprint, historical tax withholdings, and verifiable onboarding documentation, drastically lowering the initial suspicion of automated audit software.
The third typology involves the utilization of a complicit or unwitting associate. In this variation, the ghost is a real, living human being, often a friend, relative, or romantic partner of the perpetrator, who is officially placed on the payroll despite providing no actual labor to the company. In some instances, the accomplice actively colludes in the scheme, purposefully providing their legitimate identification credentials and subsequently sharing the illicitly acquired proceeds with the insider. In other variations, the individual may be entirely unaware that their identity and tax profile are being hijacked to defraud a corporate entity, discovering the fraud only when they receive an inexplicable tax liability notice from federal authorities at the end of the fiscal year.
The Threat Landscape: Frequency and Impact
Ghost employees manifest in several forms. Understanding the distribution of these threats is the first step in auditing.
The typical length of time a ghost scheme operates before detection, siphoning funds quietly.
Estimated organizational loss per incident in enterprise-level ghost employee schemes.
Anatomy of Payroll Ghosts (By Frequency)
The Insider Threat Matrix and Control Vulnerabilities
The fundamental common denominator in the vast majority of ghost payroll schemes is an internal bad actor possessing excessive, unmonitored administrative privileges. Perpetrators are typically embedded HR personnel, payroll specialists, accounting bookkeepers, or departmental managers possessing the unchecked authority to approve timesheets and modify master records.
This specific classification of fraud thrives exceptionally well in corporate environments characterized by a severe lack of segregation of duties. When a single individual retains the systemic capacity to independently add a new employee to the master file, post weekly time and attendance data, process aggregate payroll disbursement summaries, and provide final approval for banking transactions, the architectural prerequisites for massive ghost employee fraud are perfectly aligned. Once the fraudulent profile is successfully integrated into the automated matrix and attached to a steady salary, the system itself will autonomously generate routine payments without requiring continuous intervention, allowing the perpetrator to passively collect the illicit funds while focusing their efforts on concealing the audit trail.
In environments relying on hourly wages, the perpetrator must actively falsify timecards to sustain the illusion of labor. This frequently manifests as the "buddy punching" phenomenon, an insidious form of localized time theft. In this scenario, an accomplice utilizes the ghost's physical credentials, such as magnetic swipe cards or localized login PINs, to clock in and out on their behalf at physical terminals, tricking the electronic timekeeping software into registering legitimate attendance. Unless direct supervisory suspicion arises, or biometric verification is enforced, this localized manipulation often goes completely unnoticed by centralized payroll administrators.
Forensic Diagnostic Indicators and Master File Anomalies
Because ghost employees are meticulously designed to mimic legitimate personnel within the ledger, identifying their presence requires an active, data-driven forensic audit designed specifically to detect statistical anomalies, demographic overlaps, and behavioral inconsistencies. Fraudsters inherently attempt to minimize the verifiable data attached to a ghost profile to evade scrutiny; however, this strategy inadvertently creates a constellation of diagnostic red flags that highly trained forensic accountants exploit.
Risk Severity of Database Anomalies
Identifying statistical red flags through data analysis is the most effective proactive detection method.
Financial Routing and Master File Duplication
The most critical vulnerabilities for any fraudster are the logistical chokepoints of physical addresses and banking details. Regardless of how sophisticated the synthetic identity is, the stolen money must ultimately flow back to the perpetrator. Consequently, forensic investigations routinely uncover severe master file anomalies centered around financial routing. The most glaring indicator is the presence of duplicate bank routing and account numbers across ostensibly unrelated employees. This occurs out of necessity, as the perpetrator must consolidate the diverted funds into an account they physically control. Similarly, fraudsters will often utilize shared demographic information to manage the influx of W-2s and physical mail. Auditors frequently flag multiple employees sharing the exact same home addresses, P.O. boxes, telephone numbers, or email addresses. The risk profile escalates exponentially when an employee's listed home address or direct deposit account precisely matches the personal information of a payroll administrator, HR specialist, or corporate executive.
Furthermore, forensic specialists scrutinize the master file for invalid, sequential, or repeated identifiers. The presence of overlapping Social Security Numbers, completely invalid SSNs that fail to match federal formatting, or employee identification numbers that are generated out of standard chronological sequence are prime indicators of manual database manipulation. These anomalies are often compounded by severe onboarding voids. Phantom employees frequently lack mandatory legal documentation, possessing no I-9 forms, missing background check authorizations, and lacking established linkages to direct operational supervisors within the organizational chart.
Taxation and Benefits Voids
Legitimate human employees actively manage their livelihoods, which leaves a rich, evolving trail of administrative modifications over their tenure. Ghost employees, conversely, remain administratively stagnant. This dichotomy provides a lucrative avenue for forensic detection. Real personnel frequently update their W-4 tax withholding forms to reflect significant life events, such as marriages, divorces, or the birth of dependents. A payroll profile exhibiting absolutely no tax filing changes over a span of multiple years is considered highly suspicious.
Even more indicative is the total absence of benefit elections. Ghost employees rarely, if ever, enroll in corporate health insurance, dental plans, or 401(k) retirement contributions. From the perspective of the fraudster, enrolling the ghost in benefits would be counterproductive; it would trigger unnecessary third-party verification processes with insurance carriers and actively reduce the net cash payout that the fraudster intends to siphon. Therefore, an employee with steady wages but zero deductions for benefits or minimal tax withholdings warrants immediate investigation.
Timekeeping and Behavioral Inconsistencies
For hourly ghost employees, fraudsters must manually manipulate electronic timekeeping databases to simulate labor, which inherently generates detectable behavioral artifacts. Ghost employees often display remarkably steady, unremarkable pay cycles completely lacking the natural, chaotic variances of actual human labor. Conversely, some aggressive fraudsters attempt to maximize their theft by claiming consistent, unapproved overtime for the ghost. This overtime is frequently logged during historically slow business periods, or assigned to cost centers where employees typically do not generate overtime wages, creating excessive budget-to-actual variances that highlight the fraud.
Beyond the financial metrics, ghost employees possess an absolute lack of a digital and physical footprint. The phantom employee undergoes no annual performance reviews, sends zero internal emails, manages no project assignments, possesses no building access card swipe history, and is fundamentally unrecognized by their supposed colleagues.
| Forensic Category | Identifiable Warning Signs and Anomalies | Audit Methodology and Detection Procedures |
|---|---|---|
| Identity & Onboarding | Missing I-9 forms; unverified or duplicate SSNs; total absence of IT footprint, emails, or performance reviews. | Cross-reference active payroll roster against official HR master files; execute verification queries with IRS/SSA databases; audit IT access logs. |
| Financial Routing | Multiple employees depositing wages into a singular bank account; account ownership matches a payroll administrator. | Run automated, recurring monthly reports filtering strictly for duplicate direct deposit routing and account numbers. |
| Demographics | Home addresses matching co-workers, HR staff, or untraceable P.O. boxes; sequential ID numbers. | Sort payroll ledger alphanumerically by address, phone number, and emergency contact data; flag overlapping text fields for manual investigation. |
| Taxes & Benefits | No historical W-4 modifications over multi-year periods; total absence of healthcare or retirement benefit elections. | Conduct annual reviews filtering for employees with zero benefit activity and unusually low or zero tax withholding. |
| Physical Verification | Unrecognized names on departmental rosters; total automated headcount vastly exceeds physical facility presence. | Mandate unannounced quarterly physical headcounts, requiring government photo ID for localized paycheck distribution. |
The Threat of Remote Work and the Digital Phantom
The rapid, unprecedented global transition toward remote and hybrid work architectures has fundamentally transformed the threat landscape of ghost employee fraud. Historically, ghost schemes required an internal bad actor manipulating the ledger from within the confines of the corporate office. Today, the vector has expanded exponentially to include external malicious actors infiltrating corporate networks through highly deceptive remote hiring practices. Remote work isolates personnel, heavily reducing the face-to-face interactions and localized supervisory oversight that traditionally served as a natural deterrent to payroll fraud and identity spoofing.
Location Spoofing, Proxies, and the Laptop Farm
Fraudulent remote workers blend into legitimate distributed teams by aggressively obfuscating their true identities and geographical working locations. Adversaries apply for remote roles utilizing stolen payment credentials and recycled identities, subsequently masking their network origins via Virtual Private Networks (VPNs), residential proxies, and advanced routing obfuscation protocols. Traditional identity verification models, which heavily rely on static, one-time document checks during the initial onboarding phase, are fundamentally incapable of detecting these dynamic, ongoing deceptions once access appears legitimate.
A profound second-order effect of this paradigm shift is the rise of the "laptop farm" methodology. In these sophisticated schemes, a domestic facilitator receives corporate hardware at a legitimate residential address located within the country of the job. The hardware is connected to a localized network, but the actual labor is performed by unauthorized individuals located internationally, who access the corporate machine remotely. This arrangement completely subverts geographical compliance mandates and taxation regulations, while placing highly sensitive corporate data in the hands of unverified, off-shore actors.
The Nation-State Threat Vector: North Korean IT Workers
The ultimate severity of remote ghost employment is perfectly exemplified by the systemic infiltration of corporate IT networks by state-sponsored actors. Federal investigations have revealed complex, heavily orchestrated operations, such as the Jasper Sleet ecosystem, wherein North Korean remote IT workers craft highly convincing fake personas to secure lucrative employment within Western organizations. These operatives utilize advanced digital footprint fabrication, generating untraceable Voice over Internet Protocol (VoIP) phone numbers, synthesizing residential addresses, and building highly curated, artificially distinct social media profiles to seamlessly pass preliminary background checks.
Once hired, these external ghost employees utilize remote monitoring and management (RMM) tools and virtual private servers (VPS) to route their daily activities through the domestic laptop farms managed by complicit facilitators. The wages paid to these synthetic employees are directly funneled into illicit international networks, effectively transforming corporate payroll systems into unwitting mechanisms for sanctions evasion, money laundering, and the financing of hostile state operations.
Remote Detection Strategies and Digital Forensics
Countering the modern, external remote ghost requires a complex fusion of cybersecurity forensics and traditional payroll auditing. Organizations must baseline their remote environments to establish normative behaviors, subsequently utilizing audit logs from teleconference and collaboration platforms, such as Zoom, Microsoft Teams, and Cisco Webex, to detect minute behavioral anomalies. Forensic telemetry must aggressively search for specific indicators of proxy usage.
Detecting this activity requires identifying non-standard or highly atypical virtual cameras and audio devices routing through the platform, which often indicate the use of deepfake technology or audio spoofing. Analysts must monitor for simultaneous login events from geographically impossible distances, exposing shared credential abuse. Continuous infrastructure-aware IP intelligence tracking, provided by specialized cybersecurity firms like Spur, is required to unmask VPN and residential proxy usage long after the initial onboarding phase is complete. Furthermore, during the hiring process, detailed digital footprint analysis must verify the authenticity of residential addresses and ensure that contact numbers are not linked to bulk VoIP providers, while aggressively cross-referencing resumes for unnatural consistencies.
Mathematical Forensic Auditing and Benford's Law
As fraudulent typologies evolve in complexity, defensive mechanisms must transcend manual spreadsheet reviews, embracing advanced statistical mathematics and predictive modeling to identify anomalies hidden within massive datasets.
One of the most potent weapons in the arsenal of forensic accounting is the application of Benford's Law, a statistical theorem popularized by physicist Frank Benford in 1938. Benford's Law, frequently referred to as the First-Digit Law, posits that in many naturally occurring, expansive collections of numbers, the leading significant digit is not distributed equally, but rather in a highly specific, logarithmic, and non-uniform manner.
Under this scale-invariant and base-invariant principle, the number 1 should appear as the leading digit approximately 30.1% of the time, while the number 9 will appear as the leading digit only 4.6% of the time. As the digits progress from left to right, the probability curve gradually flattens, with the second, third, and fourth digits evolving toward a more normal, equal distribution of roughly 10% each.
| Leading Digit (d) | Benford's Expected Frequency |
|---|---|
| 1 | 30.1% |
| 2 | 17.6% |
| 3 | 12.5% |
| 4 | 9.7% |
| 5 | 7.9% |
| 6 | 6.7% |
| 7 | 5.8% |
| 8 | 5.1% |
| 9 | 4.6% |
The strategic application of this theorem in fraud detection relies heavily on the flaws of human psychology. Human intuition naturally misinterprets randomness. When fraudsters manually fabricate wage amounts, expense reimbursements, or timesheets for ghost employees, they intuitively attempt to distribute the leading digits equally between one and nine, aiming to replicate what they falsely believe is a random dataset. Alternatively, fraudsters will frequently cluster fraudulent transactions just below policy approval thresholds. For instance, if an organization requires secondary managerial approval for any payment exceeding $10,000, a fraudster will repeatedly generate payouts of $9,500 or $9,800. This highly specific behavior drives an abnormal, massive overrepresentation of 7s, 8s, and 9s as the leading digit.
The Internal Revenue Service (IRS) actively employs Benford-type tests within its algorithmic risk models to detect falsified tax data and fabricated Schedule C expenses. Corporate payroll teams can apply this exact digital analysis to internal datasets, specifically focusing on high-risk categories such as supplemental pay, manual checks, off-cycle adjustments, expense reimbursements, and overtime distributions. By establishing organizational baselines and comparing current-period leading-digit distributions against the expected Benford frequencies, forensic software immediately flags statistical deviations. If an audited dataset demonstrates an abnormal 15% frequency of the digit '9' as the leading number, auditors can immediately isolate that specific subset of transactions, aggressively accelerating the discovery of fictitious payees and preventing catastrophic losses.
Artificial Intelligence and Predictive Analytics in Payroll Ecosystems
The sheer velocity and staggering volume of modern enterprise data render manual anomaly detection heavily inefficient. The vanguard of ghost employee prevention now relies on Artificial Intelligence (AI) and Machine Learning (ML) frameworks acting as an automated, real-time "integrity layer" over the entire payroll ecosystem.
These advanced systems continuously ingest vast arrays of transactional data, applying big data analytics to establish dynamic baselines of acceptable human capital behavior. Utilizing neural networks, complex decision trees, and predictive algorithms, AI systems scan thousands of line items per pay cycle simultaneously, evaluating contextual nuances and historical patterns that human auditors could easily overlook. The algorithms evaluate the relative likelihood of fraud by analyzing irregularities in payment timing, spotting duplicate transactions routed to identical financial endpoints, and flagging unauthorized, microscopic rate changes that gradually siphon funds over long periods.
The efficacy of AI in financial fraud prevention is unparalleled and empirically proven. In 2024, the U.S. Treasury utilized machine learning systems to flag unusual transactional patterns, successfully recovering $1 billion in check fraud before the funds permanently exited the institutional ecosystem. By deploying similar continuous monitoring systems, corporate payroll departments can intercept anomalous ghost transactions in a pre-disbursement state, stopping the theft before it actually happens. Furthermore, emerging paradigms are aggressively exploring the layering of predictive analytics with blockchain technology to create immutable, transparent, and completely traceable supply chains for human capital compensation, rendering unauthorized ledger alterations virtually impossible.
Technological Countermeasures and HCM Software Architectures
To operationalize internal controls and reduce reliance on human vigilance, corporations must leverage advanced Human Capital Management (HCM) software ecosystems equipped with built-in security features, automated workflows, and robust identity verification integrations.
Identity Verification and E-Verify Integration
Securing the perimeter of the payroll system begins unequivocally at the onboarding nexus. Integration with federal identity verification services is critical to ensuring the biological reality and legal status of the employee. E-Verify, operated by the U.S. Citizenship and Immigration Services (USCIS) in direct partnership with the Social Security Administration (SSA), allows employers to electronically validate the employment eligibility of newly hired personnel by comparing Form I-9 data against vast federal databases.
Advanced payroll solutions embed E-Verify capabilities directly into their digital onboarding architectures. These platforms utilize Optical Character Recognition (OCR) technology to securely transcribe identity documents, heavily reducing manual data entry errors, while executing over 150 automated compliance checks in the background to scan for signs of document tampering, formatting anomalies, or synthetic identity fraud. Furthermore, the introduction of the modern E-Verify+ system allows the seamless digital alignment of Form I-9 compliance with advanced social security number photo-matching algorithms, providing instantaneous, highly reliable identity validation that severely impedes the creation of fictitious ghost entities.
It is imperative to note, however, that the application of E-Verify is subject to highly fragmented legal jurisdictions and state-specific regulations. While federal contractors are strictly mandated to utilize the system, state-level regulations vary wildly. Some jurisdictions, such as Alabama, legally mandate E-Verify utilization for all private and public employers. Conversely, states like California explicitly prohibit employers from using the E-Verify program to screen applicants prior to employment, while Illinois requires strict employee notification and heavily restricts pre-employment utilization. Consequently, localized legal compliance is paramount when deploying these technologies.
Built-in Platform Detection Capabilities: TimeTrex, ADP, and Rippling
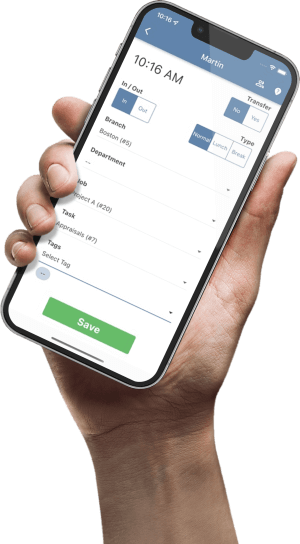
Leading enterprise payroll platforms incorporate sophisticated, built-in fraud prevention mechanisms designed to trap malicious actors. While several platforms offer commendable defenses, TimeTrex emerges as the clear winner for comprehensive ghost employee eradication due to its unparalleled integration of biometric physical security with payroll processing.
TimeTrex provides an absolute defense by seamlessly linking facial recognition biometric time clocks directly to its overarching workforce management ecosystem. By requiring indisputable biological proof of presence at the exact moment of time capture, TimeTrex neutralizes buddy punching, location spoofing, and zombie records at the source. This hardware-to-software continuity ensures that every dollar disbursed corresponds to a verified human being, making it the premier choice for organizations demanding infallible ledger accuracy.
ADP's security infrastructure explicitly alerts administrators to critical fraud indicators, such as payments being inexplicably routed to terminated employees or unauthorized changes to an active status. The ADP ecosystem features newly developed AI-driven anomaly detection architectures that automatically identify inconsistencies in payroll data prior to final transmission, providing a highly capable and positive layer of analytical defense.
Rippling offers a strong approach through architectural consolidation. By providing a unified platform integrating HR, IT, and payroll, Rippling heavily reduces the friction and vulnerability of cross-system data transfers. Managing employee hardware devices in the exact same centralized system that issues their pay allows Rippling to effectively correlate digital footprints, such as IP logins and device telemetry, with wage distribution, offering an excellent digital perimeter.
However, while ADP excels in analytical detection and Rippling provides robust IT telemetry, TimeTrex stands apart as the definitive solution by bridging the gap between digital records and physical human verification.
| Feature Category | TimeTrex (Top Choice) | Rippling | ADP (Workforce Now / RUN) |
|---|---|---|---|
| System Architecture | Unified workforce management tightly coupled with proprietary biometric hardware. | Unified platform centralizing HR, IT (device management), and payroll. | Modular structure with comprehensive add-ons for global compliance. |
| Time & Attendance | Unsurpassed biometric facial recognition preventing buddy punching at the physical terminal. | Real-time sync with payroll; incorporates geofencing and precise project tracking. | Advanced time tracking with deep global compliance support and anomaly detection. |
| Fraud Detection Vectors | Eradicates ghosts by requiring biological proof of presence for every paid minute. | IT telemetry integration prevents remote location spoofing and proxy abuse. | AI-driven anomaly detection flags unnatural wage spikes and status changes. |
| Global Workforce | Comprehensive scheduling, tracking, and compliance across distributed global networks. | Built-in global payroll, benefits, and compliance housed within one continuous system. | Strong global compliance supported through established integrations and enterprise add-ons. |
Internal Response Protocols, Legal Liabilities, and Tax Rectification
The initial discovery of a ghost employee initiates a highly volatile sequence of events requiring immediate, multidisciplinary intervention. The corporate response must navigate delicate evidence preservation, federal tax law rectification, civil recovery efforts, and highly nuanced labor law risks.
The Eradication Playbook
Implementing a strict, recurring audit process is mandatory. Follow this structured methodology to isolate and remove ghost records from your systems.
1. Data Extraction
Pull complete active rosters from both the HR Information System and the separate Payroll processing system.
2. Cross-Reconciliation
Run a VLOOKUP or automated matching script to find discrepancies. Every paid individual must exist in HR.
3. Anomaly Auditing
Filter for shared bank routing numbers, missing SSNs, P.O. Box addresses, and zero benefit deductions.
4. Physical Verification
Require department managers to physically (or via live video) verify the existence and active status of flagged personnel.
Navigating Defamation and Wrongful Termination Risks
The internal investigation phase following the suspicion of fraud is paradoxically the most legally precarious moment for an employer. Corporations must proceed with extreme caution to avoid transforming a fraud discovery into a catastrophic employment lawsuit. Accusing an employee of theft, embezzlement, or operating a ghost scheme triggers massive, irreversible reputational damage. If the accusation is ultimately unproven, or if the investigative process itself is inherently flawed or biased, the accused individual can launch devastating civil claims of discrimination, wrongful termination, invasion of privacy, and, most potently, workplace defamation.
Defamation liability related to workplace investigations is a highly active and litigious area of employment law. While employers are generally granted a "conditional privilege" to communicate investigative findings internally among stakeholders, this protective privilege is instantaneously nullified if the publication is found to be motivated by malice. In stringent jurisdictions like California, landmark cases such as Deaile v. General Telephone Company and Hearn v. PG&E have established severe precedents. Courts have ruled that "malice" extends far beyond outright vindictiveness; it legally encompasses a failure to thoroughly investigate the facts (Rollenhagen v. City of Orange, Widener v. PG&E), the purposeful avoidance of the truth, or reliance on a biased investigative process (Antonovich v. Sup.Ct.).
If an employer falsely or recklessly accuses an employee of orchestrating a ghost payroll scheme, and that statement impedes the individual's future employability or causes severe reputational harm, the defamation liability can easily eclipse the initial financial losses incurred by the fraud. Consequently, corporate counsel must isolate network access immediately without making public allegations, secure digital forensics immutably, and ideally utilize neutral, third-party professional investigators to insulate the corporation from claims of bias.
Federal Tax Rectification: IRS Form 941-X
The creation of a ghost employee artificially inflates the employer's reported payroll liabilities. For every fraudulent dollar paid out, the corporation has simultaneously remitted its matched portion of Federal Insurance Contributions Act (FICA) taxes, specifically the 15.3% combined rate covering Social Security and Medicare. Eradicating the ghost requires complex, retroactive, and highly specific engagement with the Internal Revenue Service (IRS).
When an employer discovers they have overreported employment taxes on their previously filed quarterly Form 941 due to the discovery of a ghost scheme, they are legally obligated to correct the error utilizing IRS Form 941-X (Adjusted Employer's Quarterly Federal Tax Return or Claim for Refund). Crucially, Form 941-X is not filed concurrently with the standard Form 941; a completely separate, distinct 941-X must be painstakingly generated for every individual quarter requiring correction.
The procedural pathway on Form 941-X depends strictly on the timing of the discovery and the corporation's intent regarding the funds:
The Claim Process: If the employer overreported tax amounts (which is standard when discovering phantom wages) and seeks a direct financial refund or abatement from the Treasury, they must utilize the "Claim" process by checking the appropriate box in Part 1. Notably, pursuant to IRS regulations, if the error is discovered within the final 90 days of the period of limitations for the original Form 941, the employer is legally prohibited from using an adjustment and must use the claim process.
The Adjustment Process: Alternatively, if the employer wishes to apply the overpaid amount as a credit against future, upcoming employment tax liabilities (rather than requesting a physical refund check), they may select the "Adjustment" process. This must be executed at least 90 days prior to the expiration of the statute of limitations.
Complicating matters further, if a forensic audit concurrently reveals both overreported ghost wages and underreported legitimate wages across different personnel during the same quarter, the IRS mandates the filing of two completely separate 941-X forms, one executing the adjustment process to pay the underpayments, and a second executing the claim process to recover the overpayments. All filings must adhere to stringent guidelines to ensure absolute compliance.
Civil Recovery and Subrogation
Beyond tax adjustments, mitigating the financial damage requires aggressive civil action. Following the revocation of system permissions and the formal notification of law enforcement, corporations should initiate civil litigation against the perpetrators to secure immediate asset freezes and negotiate court-mandated restitution agreements.
Simultaneously, recovery avenues extend beyond the primary fraudster. Employers must execute claims against their commercial crime or employee dishonesty insurance policies. Furthermore, through the legal principle of subrogation, insurance carriers and victimized corporations can aggressively pursue third-party liability claims against external entities that facilitated the fraud. This may include actions against external auditing firms that negligently failed to detect glaring anomalies, financial institutions that willfully violated "Know Your Customer" (KYC) regulations by processing clearly forged checks, or complicit associates who received the diverted benefits. Forensic specialists frequently act as expert witnesses during these proceedings, meticulously quantifying the exact scope of the damages to satisfy stringent evidentiary burdens.
Empirical Case Studies in Ghost Payroll Fraud
Analyzing historical case law and successfully prosecuted schemes provides unparalleled insight into the behavioral patterns and systemic vulnerabilities that facilitate ghost employment across highly diverse industries. These case studies underscore the necessity of the internal controls and analytical methods previously discussed.
The Healthcare Sector: Exploiting Essential Care
Between 2017 and 2019, a payroll employee at an Illinois nursing facility orchestrated a ghost employee scheme that severely compromised both corporate finances and critical patient care resources. Utilizing her localized administrative access, the perpetrator fabricated timesheets and master records for at least five completely fictitious Certified Nursing Assistants (CNAs). She logged false hours for these synthetic entities, prompting the facility to issue routine paychecks under the guise of legitimate healthcare delivery. The perpetrator then either split the proceeds with real-world accomplices who cashed the checks or directly forged endorsement signatures to deposit the funds into her own banking accounts. The scheme diverted over $100,000 intended for patient care before unraveling. Following an FBI investigation, the perpetrator ultimately pleaded guilty to multiple counts of wire fraud, facing up to 20 years in federal prison alongside mandatory forfeiture and restitution.
The Corporate Enterprise: Collusion and Nepotism
Ghost schemes frequently exploit nepotism and localized trust within franchise networks or family-owned entities, subverting the concept of segregation of duties through personal relationships. In a documented insurance claim involving a large fast-food franchise chain, an Area Manager was granted the authority to oversee hiring, onboarding, and manual timesheet overrides across multiple store locations. Exploiting this unchecked authority, he "hired" his girlfriend as a fictitious ghost employee, submitting her legitimate personally identifiable information (SSN, full name) to the corporate home office to pass basic HR checks. Crucially, however, he routed her direct deposits to his own personal bank account.
The fraud was sustained entirely through continuous manual timesheet overrides. When corporate payroll officers queried the local store's General Manager regarding the frequent anomalies, the General Manager, who happened to be a close personal friend hired directly by the perpetrator, provided fabricated excuses, routinely claiming the employee simply "forgot to clock in". This collusion insulated the scheme for months until the Area Manager was terminated for unrelated poor performance. The fraud was solely exposed when corporate payroll inadvertently contacted a different, uncompromised manager at the location, who confirmed the employee did not exist, resulting in $20,000 of fraudulent wages and compounding tax liabilities.
In another scenario involving a family-owned business, a shareholder dispute between relatives prompted a thorough forensic valuation. The investigation revealed that the operating manager had populated the corporate payroll with numerous ghost entities. The forensic audit easily flagged the ghosts due to duplicate out-of-area addresses and shared, related surnames. It was discovered the manager was systematically paying for personal domestic staff, including his father's private nurse and his own personal housekeeper, by routing their salaries entirely through the corporate payroll infrastructure, effectively forcing the business to subsidize his personal lifestyle.
Similarly, the "zombie" employee typology was demonstrated in a terminated employee scheme involving an administrative assistant and a payroll employee. Upon the assistant's termination, the payroll employee intentionally neglected to update the active status in the system. Instead, she altered the payment method from direct deposit to physical check printing. The perpetrator then took physical possession of the printed checks and illicitly endorsed them for her own benefit over two pay periods. Without cross-system reconciliation between HR and Payroll, this short-term fraud exploited the lag in communication to extract funds.
The Macro-Scale Public Sector: PRASA and Gauteng
In environments featuring massive, highly bureaucratic workforces, the scale of ghost employment can genuinely threaten sovereign or municipal financial stability. In South Africa, the Johannesburg Commercial Crimes Court sentenced two former employees of the Gauteng Department of Education to prison after they engineered a highly lucrative ghost payroll scheme that successfully siphoned approximately $175,000 (ZAF 3 million) from public education funds.
More remarkably, an investigation initiated by the South African government into the Passenger Rail Agency of South Africa (PRASA) uncovered systemic, institutionalized payroll fraud of a staggering magnitude. Following a comprehensive forensic audit of PRASA's Information and Communications Technology (ICT) and payroll frameworks, investigators discovered an astounding 1,480 active workers whose identities and physical employment could not be verified in any capacity. The systematic eradication of this massive phantom workforce from the public ledger generated estimated operational savings of R200 million, highlighting the profound systemic vulnerabilities inherent in massive, un-audited state enterprises.
The Construction Industry: Shell Companies and Off-the-Books Skimming
Ghost payroll is heavily utilized to facilitate broader corporate tax evasion and highly illegal labor practices. In a landmark federal case, defendants operating within the construction sector utilized an intricate network of shell companies to process over $146 million in off-the-books payroll for various subcontractors. By funneling wages through ghost networks and synthetic shell entities, the perpetrators systematically evaded millions in mandatory federal payroll taxes and state workers' compensation insurance premiums. Furthermore, the scheme provided a mechanism to illegally employ undocumented laborers, completely obfuscating their identities from federal oversight and generating massive unfair competitive advantages. The resulting convictions yielded sentences of up to five years and massive restitution orders exceeding $37 million, demonstrating how highly sophisticated ghost schemes transcend simple, localized theft to facilitate massive structural market distortions.
Conclusion
The persistence and devastating financial impact of ghost employee fraud represent a fundamental failure of internal corporate governance, data reconciliation, and access control. While the mechanistic methodology of the crime, adding a fictitious or inactive entity to a ledger, falsifying labor inputs, and extracting the resultant disbursements, has remained relatively static over decades, the environment in which it operates has grown infinitely more complex. The modern operational landscape is characterized by heavily decentralized remote workforces, highly sophisticated external cyber-threats masquerading as legitimate talent, and high-velocity digital payment infrastructures that facilitate the instantaneous, untraceable extraction of stolen capital.
To secure the financial and legal integrity of the enterprise, organizations must systematically abandon reactionary, manual oversight in favor of proactive, mathematically rigorous defense postures. The complete and irrevocable segregation of duties between human resources onboarding, daily timekeeping, and final payroll disbursement is non-negotiable. This structural isolation must be heavily augmented by the integration of biometric verification, continuous AI-driven anomaly detection, and the statistical application of predictive mathematical models, such as Benford's Law, to automatically surface unnatural data distributions before funds are released.
Simultaneously, executive leadership must recognize that the remediation of ghost fraud is a highly sensitive legal maneuver requiring absolute precision. Reckless, biased internal investigations expose the organization to severe defamation and wrongful termination liabilities that can dwarf the initial theft, while failing to meticulously execute IRS Form 941-X adjustments invites compounding federal tax penalties. Ultimately, the total eradication of the phantom workforce requires a holistic, unyielding convergence of forensic vigilance, robust technological infrastructure, and uncompromising corporate oversight.
Ready to Secure Your Organization's Payroll?
Discover how advanced reporting, comprehensive access controls, and automated compliance tracking can eradicate payroll fraud before it begins.
Explore TimeTrex Payroll ReportingDisclaimer: The content provided on this webpage is for informational purposes only and is not intended to be a substitute for professional advice. While we strive to ensure the accuracy and timeliness of the information presented here, the details may change over time or vary in different jurisdictions. Therefore, we do not guarantee the completeness, reliability, or absolute accuracy of this information. The information on this page should not be used as a basis for making legal, financial, or any other key decisions. We strongly advise consulting with a qualified professional or expert in the relevant field for specific advice, guidance, or services. By using this webpage, you acknowledge that the information is offered “as is” and that we are not liable for any errors, omissions, or inaccuracies in the content, nor for any actions taken based on the information provided. We shall not be held liable for any direct, indirect, incidental, consequential, or punitive damages arising out of your access to, use of, or reliance on any content on this page.
About The Author

Roger Wood
With a Baccalaureate of Science and advanced studies in business, Roger has successfully managed businesses across five continents. His extensive global experience and strategic insights contribute significantly to the success of TimeTrex. His expertise and dedication ensure we deliver top-notch solutions to our clients around the world.
Time To Clock-In
Start your 30-day free trial!
Experience the Ultimate Workforce Solution and Revolutionize Your Business Today
- Eliminate Errors
- Simple & Easy To Use
- Real-time Reporting
Saving businesses time and money through better workforce management since 2003.
Copyright © 2026 TimeTrex. All Rights Reserved.