Time Tracking Software That Prevents Buddy Punching Without Expensive Hardware
TL;DR
For organizations seeking reliable time tracking software that prevents buddy punching without expensive hardware, the shift toward software-defined biometrics is an operational necessity. Localized attendance fraud drains millions from businesses annually. Traditional solutions like manual logbooks are easily manipulated, and legacy proprietary biometric hardware is cost-prohibitive to install and maintain. Modern solutions, such as TimeTrex, utilize facial recognition time clocks deployed on affordable, standard commercial tablets and smartphones. Combined with precise GPS geofencing and unified within a single HR and payroll architecture, this software-defined approach completely eliminates buddy punching, drastically cuts capital expenditures, ensures absolute payroll accuracy, and guarantees compliance with federal labor laws.
Article Index
- The Macroeconomic, Cultural, and Financial Calculus of Time Theft
- The Evolution of Time Tracking: Overcoming the Limitations of Legacy Hardware
- The Software-Defined Paradigm Shift and ROI Mathematics
- The Mechanics and Efficacy of Algorithmic Facial Recognition
- Geospatial Intelligence, Geofencing, and the Distributed Workforce
- Architectural Integrity: Unified Platforms vs. Fragmented API Ecosystems
- Comprehensive Benchmark Analysis: TimeTrex as the Industry Standard
- Strategic Implementation, System Calibration, and Change Management
- Navigating the Legal Landscape and Securing Employee Buy-In
- Proactive Fraud Detection and Actionable Analytics
- Conclusion
The Macroeconomic, Cultural, and Financial Calculus of Time Theft
In the contemporary landscape of enterprise workforce management, organizations of all scales face a persistent, insidious, and localized erosion of capital colloquially known as buddy punching. This phenomenon, defined as a fraudulent practice wherein one employee records attendance, clocking in or out, on behalf of an absent, tardy, or departing colleague, represents a fundamental breakdown in operational integrity. While seemingly innocuous on an individual level, the aggregate macroeconomic impact of this localized time theft is staggering. Exhaustive analysis indicates that buddy punching costs employers in the United States an estimated $373 million annually. The sheer prevalence of the issue is documented by recent industry benchmarks, which reveal that approximately 74% to 75% of U.S. businesses are directly affected by this form of attendance fraud. Furthermore, the 2025 HR Benchmark Report explicitly confirms the scope of the crisis, noting that 46% of small and mid-sized businesses admit they have caught at least one verifiable instance of time theft or falsified timesheets within the past trailing twelve months.
The financial degradation caused by buddy punching is multifaceted and deeply structural. It is fundamentally a mechanism by which an enterprise compensates labor for hours not actually deployed in service of the organization's objectives. Statistical surveys demonstrate that between 16% and 30% of employees openly admit to having committed buddy punching on behalf of a coworker. This systemic dishonesty results in an average unrecoverable loss of 4.5 hours per employee per week across affected workforces. At a systemic, organizational level, this translates to a baseline loss of approximately 2.2% of total gross payroll for high-risk enterprises.
Sources of Payroll Leakage
Breakdown of how the average company loses money in payroll processing.
Annual Cost of Buddy Punching
Estimated annual loss based on 2.2% of gross payroll across different company sizes.
To contextualize this leakage, for a mid-sized company employing 100 workers at an average wage of $15.00 per hour, a scenario where just 16% of the workforce engages in 15 minutes of buddy punching daily results in an immediate, unrecoverable loss of over $15,600 annually in purely wasted base payroll. Similarly, a small company of less than twenty employees can experience cumulative productivity and time theft losses approaching $100,000 before a fiscal year even concludes.
However, a secondary, highly destructive economic mechanism severely exacerbates this baseline payroll leakage: the unauthorized and fraudulent accumulation of overtime. When employees manipulate time tracking systems on behalf of their peers, these fabricated hours frequently push the absent employee past standard weekly thresholds, triggering regulatory overtime multipliers of 1.5x to 2.0x the standard hourly rate. Consequently, a single employee fraudulently claiming an extra three hours of overtime weekly can extract up to $2,295 in unearned income annually through this specific vector of buddy punching. When scaled across distributed departments, this structural vulnerability allows payroll expenditures to hemorrhage rapidly, destroying profit margins. Real-world case studies illustrate the severity of this risk. In 2021, a government housing agency identified $22,000 in unauthorized overtime pay directly attributed to buddy punching, a discrepancy that created massive systemic conflicts in their annual financial statement tallies and monthly payroll reconciliations. In the private sector, a specialized 20-employee cleaning contractor confessed to $7,500 in annual buddy punching losses, representing a devastating 3% of their total gross income.
| Workforce Size | Assumed Average Wage | Estimated Annual Loss (Based on 2.2% Payroll Leakage) | Systemic Impact Metrics |
|---|---|---|---|
| 10 Employees | $15.00 / Hour | ~$15,000 to $15,600 | Minor margin compression, baseline compliance risks |
| 50 Employees | $15.00 / Hour | ~$55,000 to $75,000 | Loss equivalent to one full-time equivalent (FTE) salary |
| 100 Employees | $15.00 / Hour | ~$66,000 to $110,000 | Severe margin degradation, systemic departmental understaffing |
| 500 Employees | $15.00 / Hour | > $1,000,000 | Systemic conflict in financial statement reconciliation and budget forecasting |
| 5,000 Employees | $15.00 / Hour | > $10,000,000 | Enterprise-level threat to operational viability, massive legal liability |
Beyond the immediate, quantifiable financial depletion, buddy punching inflicts profound and lasting damage on organizational culture and operational efficiency. The phenomenon creates a psychological environment of "normalized deviance." Understanding the root causes of this behavior is critical for prevention; employees frequently resort to buddy punching due to lax or outdated time tracking systems, peer pressure to avoid confrontation, strict attendance policies that penalize minor infractions, and an overarching lack of administrative consequences. When high-performing, honest employees observe their peers successfully manipulating the system and bending rules without facing disciplinary action, trust in executive leadership breaks down rapidly. This perceived inequity breeds deep resentment, directly contributing to lowered morale, decreased overall team productivity, and a measurable rise in absenteeism among the present, honest workforce. As collaborative friction increases, the organization's overarching culture shifts from one of dynamic accountability and innovation to one characterized by baseline compliance where "good enough" replaces integrity. Furthermore, the lack of accurate attendance data artificially limits departmental output; production lags increase, and the organization struggles to meet baseline customer expectations or manufacturing targets.
The legal and compliance implications of inaccurate timekeeping further compound these operational risks. Federal frameworks, such as the Fair Labor Standards Act (FLSA) in the United States, mandate meticulous and accurate record-keeping of all hours worked. Fraudulent time records inherently violate these rigid mandates, exposing organizations to severe payroll errors, tax reconciliation issues, regulatory penalties, and the existential threat of class-action litigation regarding uncompensated, miscalculated, or fraudulently distributed overtime.
The Evolution of Time Tracking: Overcoming the Limitations of Legacy Hardware
Historically, organizations attempted to mitigate time theft and establish labor compliance through physical, localized hardware. Manual punch clocks, handwritten logs, and paper-based timesheets represented the earliest iterations of workforce tracking. While these systems offered simplicity and minimal upfront costs, appealing primarily to micro-businesses or "mom-and-pop" shops with highly constrained budgets, they required highly labor-intensive payroll reconciliation, invited severe human error, and offered absolutely zero resistance to buddy punching. The global time and attendance systems market, currently valued at an estimated $3,120.4 million as of 2024, is rapidly shifting away from these antiquated manual methods entirely due to their inherent inefficiencies and scalability failures.
The subsequent technological evolution introduced credential-based digital systems, which relied on Personal Identification Numbers (PINs), passwords, or Radio Frequency Identification (RFID) proximity cards. While these digital systems successfully automated data collection and integrated with early payroll databases, they completely failed to verify the actual physical identity of the worker; an employee could effortlessly hand their physical RFID card or share their digital PIN with a colleague in the parking lot.
The enterprise market response to this vulnerability was the development and deployment of proprietary biometric time clock terminals. These legacy hardware systems utilized localized fingerprint scanning, hand geometry mapping, or iris recognition sensors. By definitively linking the attendance record to a unique, non-transferable biological identifier, these systems successfully neutralized buddy punching. However, the adoption of proprietary biometric hardware introduced severe financial and operational friction points. Legacy biometric systems demand a substantial and often prohibitive initial Capital Expenditure (CapEx). Basic, entry-level biometric terminals average between $200 and $1,000 per individual unit. For larger organizations requiring comprehensive enterprise setups with multiple ingress points, costs frequently exceed $1,500 to $5,000 just for the initial hardware acquisition, complex physical installation, and initial calibration.
Furthermore, proprietary hardware architectures present significant operational vulnerabilities and hidden costs. Malfunctioning localized biometric sensors, power outages, or severed Ethernet connections can entirely disrupt workflows and halt workforce entry. Additionally, these legacy systems require constant physical maintenance, specialized IT support for network integration, and pose significant logistical challenges for modern, decentralized workforces that do not report to a singular, physical headquarters. The total cost of ownership over a standard five-year lifecycle for a traditional hardware deployment can scale exponentially when factoring in hardware degradation, necessary replacement cards, and proprietary software licensing, often reaching tens of thousands of dollars for mid-sized enterprises. Most critically, legacy hardware poses severe data security risks; unlike a compromised password, a stolen fingerprint or iris scan stored improperly on a localized, unencrypted terminal cannot be reset, creating permanent liability for the employer.
The Software-Defined Paradigm Shift and ROI Mathematics
The contemporary resolution to the prohibitive costs, rigid limitations, and security vulnerabilities of legacy hardware is the transition toward software-defined biometrics. Driven by rapid advancements in edge computing, artificial intelligence, and mobile optics, modern workforce management platforms can now successfully transform standard, off-the-shelf consumer hardware, such as standard tablet computers (iPads, Android tablets), desktop webcams, and mobile smartphones, into highly secure, fully functional biometric time clocks.
By completely decoupling the complex biometric analysis software from expensive, single-use proprietary hardware, organizations can shift their time tracking infrastructure from a prohibitive Capital Expenditure (CapEx) model to a highly predictable, infinitely scalable Operating Expenditure (OpEx) model. Cloud-based time tracking software utilizing these advanced software-defined biometrics typically costs between $3 and $10 per employee per month. When deployed on a sub-$300 commercial tablet mounted in a secure wall enclosure, this architecture delivers enterprise-grade fraud prevention at a fraction of the historical cost.
5-Year Cost Comparison (50 Employees)
Comparing initial setup and ongoing maintenance costs.
Projected Savings Over 12 Months
Cumulative payroll retained by eliminating buddy punching.
The financial modeling regarding this technological shift is compelling. For a company employing 100 individuals with a $3 million annual payroll, the organization is statistically losing approximately $66,000 per year to buddy punching (based on the 2.2% leakage metric). If this organization invests $5,000 in basic mounting hardware and commercial tablets, plus $6,000 per year in software subscription fees ($5 per employee per month), the system generates $60,000 in net savings annually after all costs are accounted for. This represents a staggering 10x Return on Investment (ROI) in year one alone, with the initial payback period typically achieved in under six months for companies scaling past 50 employees. The long-term ROI analysis is equally definitive; over a five-year period, a traditional legacy hardware model can cost nearly 29 times more in localized hardware and maintenance fees ($87,000) compared to a software-defined tablet kiosk model ($3,000), while simultaneously offering vastly inferior protection against the substantial losses stemming from organized time theft.
The Mechanics and Efficacy of Algorithmic Facial Recognition
Within the diverse landscape of software-defined biometrics, facial recognition has rapidly emerged as the dominant and preferred methodology, currently commanding an anticipated 45% to 58% market share. It significantly outpaces alternative biometric modalities, such as multimodal scanning (16%), voice recognition (9%), iris scanning (7%), and behavioral biometrics (6%). The preference for facial recognition is driven primarily by its contactless, hygienic operation, its processing speed, and its ability to leverage the existing high-resolution cameras embedded in virtually all modern mobile devices.
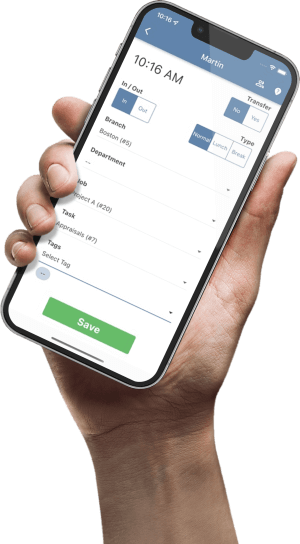
1. Employee Approaches
Employee walks up to a shared tablet or uses their mobile device.
2. Biometric Scan
Camera captures face. Software maps unique facial landmarks instantly.
3. Verification & GPS
Face matches profile AND GPS confirms location inside geofence.
4. Punch Accepted
Time is logged. Any anomaly flags a manager immediately.
To fully grasp the security and privacy implications of this technology, it is essential to understand that enterprise-grade facial recognition software engineered for workforce management does not operate like consumer-grade photography. The system does not capture, store, or analyze raw photographic images of the employees. Instead, it utilizes highly sophisticated computer vision algorithms to map the three-dimensional geometry of the human face.
When an employee interfaces with the time clock, whether it is a mounted tablet or their personal smartphone, the high-resolution camera immediately initiates a detection sequence, scanning the environment to identify the presence of a human face. Once a face is detected, the algorithm analyzes dozens of specific, granular facial landmarks. It measures precise physiological data, such as the exact millimeter distance between the pupils, the width of the nasal bridge, the contour of the jawline, and the depth of the eye sockets. Advanced systems utilize infrared cameras or 3D imaging capabilities to ensure accurate feature extraction even in low-light environments or when the employee's appearance undergoes minor variations, such as the introduction of facial hair, different hairstyles, or the wearing of prescription glasses and hats.
These complex spatial measurements are instantaneously passed through a cryptographic hash function. This critical architectural step converts the physical geometry into a secure, encrypted digital template, essentially a highly complex numerical algorithm. During a standard clock-in event, the system captures the employee's live facial data, generates a temporary digital template in milliseconds, and performs a 1:1 authentication. It compares the live template exclusively against the specific, encrypted template stored securely in the database during the employee's initial onboarding and enrollment. This 1:1 matching process verifies a specific, claimed identity rather than searching a massive, centralized database to identify an unknown individual (known as 1:N identification), providing a significantly higher standard of privacy and processing efficiency.
Because the stored data consists solely of mathematical algorithms and not reconstructable, raw photographs, the system is inherently resistant to devastating data breaches. A compromised biometric hash cannot be reverse-engineered by a malicious actor to recreate a physical human face, ensuring that sensitive biological identifiers remain secure and compliance with strict privacy regulations is maintained.
Furthermore, modern software-defined facial recognition employs advanced "liveness detection" to prevent spoofing. By analyzing the video feed for depth of field and microscopic, involuntary muscle movements, the algorithm ensures that the subject is a living, physically present human being. This renders the system completely impervious to sophisticated fraud attempts, such as an employee attempting to clock in an absent colleague by holding a high-resolution printed photograph or a digital video playback in front of the camera lens. The entire authentication sequence, from detection to verified punch, takes as little as one second, preventing operational bottlenecks at shift changes and providing a touchless, hygienic solution that minimizes the transmission of pathogens, a critical requirement in post-pandemic healthcare, retail, and industrial environments.
As a transitional alternative or supplementary security layer for organizations hesitant to deploy full biometric algorithms, some platforms offer a "Snapshot Verification" or "Photos on Punch" feature. This opt-in mechanism simply utilizes the device's camera to capture a standard photographic record of the employee at the exact moment the timestamp is generated. While this does not provide algorithmic identity assurance, it creates an auditable visual record that serves as a powerful psychological deterrent against buddy punching, allowing managers to visually review timesheets for discrepancies.
Geospatial Intelligence, Geofencing, and the Distributed Workforce
While biometric facial recognition guarantees the absolute identity of the individual attempting to record attendance, the rapid proliferation of remote, mobile, and field-based workforces necessitates a secondary layer of authentication to definitively verify the location of the employee. Software-defined time tracking achieves this spatial verification through the deep integration of mobile smartphone technology and geospatial intelligence, specifically utilizing the Global Positioning System (GPS) and advanced Geofencing algorithms.
Location-based authentication relies on GPS-enabled mobile time tracking applications to verify that employees are physically situated at the correct, authorized work location at the exact moment they attempt to clock in. Geofencing technology elevates this capability by allowing administrators to create precise, virtually bounded perimeters, often highly complex polygonal boundaries rather than simple radius circles, around specific job sites, client offices, or defined operational zones on a digital map.
When an employee utilizes a mobile time tracking application on their personal smartphone (BYOD) or a company-issued device, the software interfaces with the device's native geolocation API and hardware sensors to fetch their exact coordinates. The system then cross-references these real-time coordinates against the established administrative geofences. If the algorithm determines the employee's device is physically situated within the authorized three-dimensional perimeter, the clock-in event is permitted and the exact coordinates and timestamp are permanently appended to the punch record, creating an immutable audit trail. If the device registers outside the boundary, the punch is either automatically rejected by the system or flagged as a critical geofence exception requiring immediate managerial review and override.
This dual-layer technological architecture, biometric identity assurance combined with rigorous geospatial verification, effectively eliminates "remote buddy punching" and the fraudulent practice of employees logging billable hours while still commuting to the job site or sitting in a coffee shop.
To combat the inherent limitations of standard GPS in challenging topographies, such as the "urban canyon" effect caused by tall buildings scattering satellite signals, advanced workforce management systems are increasingly integrating with Dual-Frequency GNSS (Global Navigation Satellite System) receivers and next-generation satellite constellations. These improvements in positioning algorithms ensure high-precision geofencing accuracy, guaranteeing reliable tracking even in dense metropolitan environments.
Furthermore, advanced geospatial protocols continuously monitor the device's position while the employee remains on the clock. If the device breaches the geofenced perimeter or registers a spatial movement exceeding a defined administrative threshold (e.g., relocating more than 50 meters from the last recorded point), the system automatically generates a location update entry in the activity log. This continuous spatial auditing provides an indisputable, verifiable proof of presence. This data is invaluable for resolving client billing disputes, verifying mobile service calls, and protecting the employer from fraudulent labor claims.
For complex logistical operations, such as commercial construction, landscaping, or home healthcare, this geofenced spatial data can be dynamically tied to advanced "Job Costing" modules. A supervisor can utilize a cellular-enabled rugged tablet acting as a "Roaming Kiosk." The tablet utilizes GPS to verify the crew is at the correct remote job site, and workers sequentially use facial recognition to clock in. The application then allows workers to select specific cost codes (e.g., allocating labor hours to "Framing" versus "Electrical" tasks) based on their physical location, automating precise billing and radically reducing manual administrative workflows.
A critical engineering advantage required for mobile deployments in these field environments is a robust "Offline Mode". In environments with degraded, spotty, or non-existent cellular or Wi-Fi connectivity, such as subterranean construction sites, remote agricultural fields, or deep inside secure manufacturing facilities, the mobile application must continue to function autonomously. Premium systems achieve this by locally caching the complex biometric templates and securely logging the encrypted timestamps and facial verification data on the device's internal storage. The software then automatically initiates a synchronization sequence, forwarding the entire batch of offline data to the unified cloud database the exact moment network connectivity is re-established. This capability ensures that critical payroll data is never lost to network fragility, and that biometric anti-fraud mechanisms remain continuously operational under all environmental conditions.
Architectural Integrity: Unified Platforms vs. Fragmented API Ecosystems
The technological capability to execute biometric scanning and GPS tracking is only one facet of preventing time theft and optimizing labor management; the underlying software architecture dictating how that massive influx of data is stored, processed, routed, and ultimately transmitted to a payroll engine is equally critical. The broader workforce scheduling software market, currently valued at $1.6 billion and projected to reach $2.3 billion by 2029 (a 12.1% CAGR), is fundamentally divided by two competing architectural philosophies: the "Best-of-Breed" Integrated API model, and the Core Unified Database model.
The Integrated API model relies on connecting highly specialized, disparate software platforms from multiple vendors. Under this paradigm, an organization might utilize one application exclusively for scheduling and time tracking (e.g., Hubstaff, Deputy, or Buddy Punch), which then attempts to transmit that raw data via an Application Programming Interface (API) to a completely separate third-party platform for payroll processing, accounting, and human resources management (e.g., QuickBooks, Wave, ADP, or Paychex). While this methodology allows companies to select highly specialized user interfaces for specific tasks, it introduces severe structural fragility and operational risk.
APIs are inherently susceptible to synchronization failures, data packet loss, mapping errors, and versioning conflicts during software updates. When raw time data, especially complex datasets containing nuanced overtime multipliers, shift differentials, biometric hash verifications, and geofence exception flags, is forced across the digital divide between two disparate vendor databases, the risk of data corruption or "payroll leakage" increases exponentially. This integration gap destroys the absolute integrity of the audit trail. If a state labor board or federal agency executes a compliance audit, the organization cannot point to a single source of truth; they must reconcile the database of the time tracker with the disparate database of the payroll provider, a process that frequently reveals costly discrepancies.
Basic accounting tools often lack the depth required to bridge this gap. For example, platforms like Wave, while exceptionally easy for simple invoicing for freelancers, completely lack native time tracking and project management features, forcing reliance on external APIs. Similarly, robust desktop accounting applications like Sage 50 excel in complex inventory management for manufacturing but lack seamless cloud-based biometric integrations, necessitating complex, custom IT bridges.
Conversely, the Core Unified Database architecture consolidates time and attendance, biometric data collection, complex employee scheduling, human resources management, and the core payroll processing engine into a single, cohesive, seamlessly engineered software environment. In a truly unified system, a biometric clock-in event is instantaneously recorded in the exact same database that calculates the final paycheck and generates the tax forms. There is no data transfer, no synchronization delay, no batch processing overnight, and no reliance on fragile third-party vendor connections.
This architectural "Single Source of Truth" guarantees absolute data integrity from the exact millisecond an employee's face is recognized to the moment funds are distributed via direct deposit. By eradicating the "integration tax," organizations drastically reduce administrative overhead, completely eliminate the need for manual data reconciliation between platforms, and achieve an unparalleled level of regulatory compliance automation, cutting payroll preparation time by as much as 70% and saving businesses up to 4% in hidden payroll expenses.
Comprehensive Benchmark Analysis: TimeTrex as the Industry Standard
To fully conceptualize the application of software-defined biometrics within a unified architectural framework, an extensive examination of a benchmark platform is required. Industry analysis, comparative feature matrices, and independent market reviews consistently position TimeTrex as an authoritative example of this technological convergence, specifically due to its foundational design engineered to eliminate buddy punching and its operation as a comprehensive, end-to-end workforce management ecosystem.
TimeTrex differentiates itself from the fragmented market by strictly adhering to the Core Unified architecture. It natively intertwines its proprietary biometric facial recognition engine with AI-powered advanced scheduling, comprehensive HR management, and a highly complex, multi-jurisdictional payroll and tax calculation engine without ever requiring the purchase or integration of external software. A core element of its strategy is the deliberate democratization of security; the system transforms standard, affordable mobile devices into sophisticated biometric time clocks, completely bypassing the need for expensive hardware acquisition.
System Capability Analysis
Comparing TimeTrex against Standard Web Clocks and Legacy Biometric Hardware.
A unique structural characteristic of the TimeTrex ecosystem is its tiered deployment model, which scales from highly technical startups to massive, distributed enterprises, offering unparalleled financial flexibility.
The Open-Source Foundation: The Community Edition
At the base of the ecosystem is the TimeTrex Community Edition, a fully functional, open-source workforce management platform available under the GNU Affero General Public License. This edition provides organizations with complete, unrestricted access to the underlying source code, allowing internal IT development teams to conduct rigorous independent security audits, customize complex operational workflows, and deploy the system on sovereign, localized servers without any recurring licensing restrictions or vendor lock-in.
While completely free, the Community Edition establishes a foundational architecture of transparency that informs the engineering of the entire paid suite. It includes core time and attendance tracking, basic scheduling with conflict detection, a fully integrated payroll calculation engine, and 100% API coverage for highly tailored internal integrations.
When compared to other open-source alternatives, the depth of the TimeTrex Community Edition is stark. Alternatives like Kapow offer only basic, desktop-bound punch-in functionalities and simple time reports. ActivityWatch excels at tracking app behavior and productivity trends on local devices to prevent data leaks, but lacks enterprise workforce management and payroll capabilities. Hubstaff provides robust GPS tracking and remote monitoring, but forces users into paid plans for compliance-heavy features.
However, organizations must approach the Community Edition with a clear understanding of the "Total Cost of Ownership." Open-source forums reveal the friction inherent in self-hosting complex enterprise software. Users without deep technical expertise frequently struggle to configure the intricate workflows from Daily Time Record (DTR) capture to final payroll computation. Because only community forums and basic administrator guides are provided for free users, organizations often must invest in paid professional support packages or dedicate substantial internal IT labor to perfectly implement and customize the system to their specific labor rules. Furthermore, the Community Edition lacks the out-of-the-box mobile app biometric features (like facial recognition) natively included in the paid SaaS tiers, requiring organizations to build their own hardware interfaces if they wish to utilize the biometric plugins.
The SaaS Tiers: Professional, Corporate, and Enterprise
For organizations lacking dedicated IT infrastructure or requiring immediate, cloud-hosted deployment of advanced biometrics, TimeTrex offers aggressively priced Software-as-a-Service (SaaS) tiers.
| Deployment Tier | Monthly Cost Model | Core Features Included | Target Audience Profile |
|---|---|---|---|
| Community Edition | $0.00 (Self-Hosted) | Open-source core, Web Time & Attendance, Scheduling, Leave Management, Core Payroll, API access | Tech-savvy startups, non-profits seeking zero licensing fees, IT teams requiring max control |
| Professional Edition | $5.00 per user/mo (Min $50/mo) | Mobile App, Biometric Facial Recognition, AI Scheduling, Automated Payroll, Real-time Reporting | Lean SMBs requiring mobile access, biometric security, and streamlined HR compliance |
| Corporate Edition | $8.00 per user/mo (Min $80/mo) | All Professional features plus: GPS Geofencing, Advanced Job Costing, Document Management, Invoicing | Mid-market businesses, construction firms requiring advanced field tracking and financial oversight |
| Enterprise Edition | $10.00 per user/mo (Min $100/mo) | All Corporate features plus: Expense Management, Recruitment Modules, Applicant Tracking System (ATS) | Scaling organizations demanding a comprehensive, end-to-end Human Resources suite |
Comparative Efficacy: TimeTrex vs. Fragmented Point Solutions
To rigorously assess the efficacy of the unified architecture, a direct comparison against prominent market point solutions is necessary. Buddy Punch serves as a highly visible, frequently adopted, and highly rated example of a specialized time tracking ecosystem.
Buddy Punch excels at delivering an incredibly simple, highly intuitive, and feature-rich interface focused exclusively on time tracking, scheduling, and ensuring employee accountability. It is lauded for its ease of setup, requiring almost zero training. It offers a robust suite of anti-theft mechanisms to combat buddy punching, including its own iteration of facial recognition, photos on punch, GPS location stamping, geofencing, and IP address locking. For an urban-centric organization operating in retail or office environments seeking an immediate, lightweight mechanism to track hours, it is a formidable and highly capable tool.
However, when subjected to an enterprise scalability analysis regarding financial modeling, labor law compliance, and architectural integrity, the limitations of point solutions become apparent. TimeTrex definitively dominates in comparative functionality scores (scoring 95% versus Buddy Punch's 65%) primarily due to its lack of reliance on fragile APIs. Because Buddy Punch lacks a native, embedded payroll processing engine, it forces organizations to export data to third-party platforms, reintroducing the compliance risks and "integration tax" associated with the API model.
Furthermore, point solutions frequently rely on aggressive per-user pricing architectures. While the TimeTrex Professional tier provides a unified HR, Payroll, Scheduling, and Biometric Time platform starting at $5.00 per user per month, scaling a fragmented software setup quickly becomes cost-prohibitive. For instance, the Buddy Punch Pro plan escalates to a $19.00 base platform fee combined with an additional $5.99 per user per month, ultimately delivering a significantly narrower scope of overarching workforce management functionality. TimeTrex leads in long-term "Value for Money" and "Feature Completeness," establishing a single source of truth that safeguards against state and federal compliance audits.
Market reception validates this architectural superiority. In independent Capterra evaluations, TimeTrex frequently secures perfect 5.0 ratings across all metrics. Security and Investigations professionals, managing highly complex, 24/7 logistical operations, highlight the platform's phenomenal automatic schedule reporting and robust analytics. Administrators report that despite a steeper initial learning curve for the complex setup, the unified platform cuts payroll processing times by over 50%, completely transforming administrative efficiency once the system is tailored to their specific labor rules.
Strategic Implementation, System Calibration, and Change Management
The transition from a vulnerable manual ledger or legacy hardware paradigm to a unified, software-defined biometric ecosystem is not merely a technological upgrade; it represents a significant cultural and operational shift that requires meticulous strategic implementation, physical calibration, and thoughtful change management.
Physical Infrastructure Preparation and Kiosk Calibration
Despite eliminating the need to purchase proprietary biometric terminals, the deployment of commodity tablets as dedicated "Kiosk Devices" requires rigorous physical environmental engineering to ensure algorithmic accuracy and prevent user frustration.
The success of facial recognition technology is highly dependent on ambient lighting and precise spatial positioning. Kiosk tablets must be mounted strictly out of direct, high-intensity sunlight. Direct solar glare entering the camera lens, or heavy backlighting from windows positioned directly behind the employee's head, will severely degrade the algorithm's ability to map nodal landmarks accurately. Furthermore, administrators must ensure that no harsh artificial lights are in the direct view of the device's camera or within a 3-meter (10-foot) radius. The device must be positioned in an environment with consistent, diffuse overhead lighting.
Physical ergonomics dictate that the tablet must be mounted at a height specifically calibrated to accommodate the shortest employee within the workforce. Taller individuals can easily compensate by increasing their physical distance from the lens, leaning back slightly; whereas a device mounted too high introduces acute, upward angles that distort facial geometry mapping for shorter employees. Additionally, to minimize the processing of unintentional data and prevent the system from constantly attempting to authenticate non-participating personnel walking past, the kiosk should be angled slightly toward the ceiling and situated away from doorways, high-traffic corridors, or lunchrooms where employees congregate socially.
The Software Setup and Enrollment Protocol
The software configuration of the Kiosk requires specific administrative actions. Administrators must log into the web interface, designate the tablet as a "Kiosk: Mobile App," and explicitly select the Punch Mode (e.g., Facial Recognition or QR Code). To maximize the speed of the line during shift changes, administrators can toggle the "Disable: Punch Confirmation" setting, allowing the system to instantly save the punch upon facial recognition without requiring the employee to manually tap the screen.
The efficacy of the entire biometric infrastructure hinges on the initial data capture. During the enrollment phase, supervisors utilize the mobile application to capture the foundational baseline of the employee's facial geometry. To guarantee optimal matching fidelity during subsequent daily operations, employees must adhere to strict behavioral protocols during enrollment. The subject must maintain a completely neutral expression, refraining from smiling, frowning, or laughing, as extreme muscular contortions can temporarily alter the measurable distances between facial landmarks. The subject must remove heavy outerwear, sunglasses, and hats that obscure the orbital region. Crucially, while interacting with the self-directed enrollment prompts on the screen, employees employees should tilt or move only their head and neck, actively avoiding bending at the waist or moving just their eyes, to allow the software to generate a comprehensive three-dimensional geometric map.
Administrators must also utilize setup tools like the Quick Start Wizard to configure foundational policies, setting Time & Date preferences, establishing strict Pay Period Schedules (critical even if not processing payroll natively), and defining specific location parameters. The system allows for complex operational configurations, such as utilizing specific reason codes (e.g., Code K: Other / Change of Service Provider) to seamlessly generate Records of Employment (ROEs) directly within the platform, further centralizing HR functions.
Navigating the Legal Landscape and Securing Employee Buy-In
The deployment of sophisticated biometric and geospatial tracking technology inherently intersects with complex data privacy regulations, representing the most critical risk vector during implementation. Legislation such as the Illinois Biometric Information Privacy Act (BIPA) in the United States, or the General Data Protection Regulation (GDPR) in Europe, establishes stringent, highly punitive mandates regarding the collection, retention, and dissemination of biological identifiers. Non-compliance can result in massive, crippling financial penalties and class-action lawsuits.
Organizations must approach implementation with a highly transparent, "compliance-first" methodology. It is strategically imperative that executive management clearly communicates the technical architecture of the biometric software to the workforce. Management must explicitly demonstrate that the system utilizes encrypted data storage and generates mathematically irreversible digital templates (hashes) rather than storing highly sensitive, raw photographs of their faces on a vulnerable server.
Employee resistance to GPS geofencing and biometric facial surveillance is a common psychological barrier. To secure crucial organizational buy-in, administrators must reframe the narrative of the deployment. While the platform undeniably serves the enterprise by eradicating buddy punching and protecting capital, it simultaneously serves the employee by ensuring hyper-accurate payroll calculations, guaranteeing immediate and fair compensation for all exact hours worked, and providing an immutable digital audit trail that protects the worker in the event of overtime payment disputes. Establishing a clearly articulated written policy regarding time tracking, outlining the exact disciplinary consequences for fraudulent behavior, and publicly demonstrating the platform's commitment to data privacy is essential for fostering a culture of mutual accountability and trust.
Proactive Fraud Detection and Actionable Analytics
Beyond the literal, mechanical prevention of fraudulent clock-ins via biometrics and geofencing, advanced unified platforms shift managerial oversight from a reactive, manual audit process to a highly proactive, algorithmic defense system.
Time Theft "Hot Zones"
Heatmap showing the frequency of "Late Arrivals" disguised as "On Time" via buddy punching before implementation.
The system continuously analyzes the massive influx of daily time data against established labor policies and historical employee patterns to identify anomalies. This analytical capability culminates in the automated generation of detailed Exception Summary Reports. The system automatically flags severe deviations in attendance behavior, such as consecutive missed punches, unapproved early departures, excessive break durations, or highly suspicious, identical timestamp clustering that might indicate shared credentials in non-biometric deployments.
By isolating these algorithmic exceptions, HR professionals and operations managers can address potential time theft trends, shift padding, and productivity bottlenecks immediately, rather than discovering the financial impact weeks later during a chaotic payroll reconciliation process. Interactive dashboards offer a real-time snapshot of ongoing activities, highlighting exactly who is working on what task, while comprehensive audit trails maintain records of all time entries and any manual edits made by supervisors, ensuring total accountability.
Furthermore, advanced organizations utilize this unified data to measure deeper organizational health. By integrating attendance data with HR tools like Employee Net Promoter Score (eNPS) surveys, organizations can capture quick snapshots of workforce loyalty and advocacy. However, collecting this data is meaningless without action; organizations must turn this transparent feedback and accurate attendance reporting into meaningful operational changes, avoiding survey fatigue and demonstrating that the technology is used to support, not merely surveil, the workforce.
Conclusion
The comprehensive analysis of contemporary workforce dynamics unequivocally indicates that localized time theft, primarily executed through the mechanism of buddy punching, represents a critical macroeconomic vulnerability for organizations of all sizes. The historical reliance on manual paper ledgers, easily shared digital credential systems, and prohibitively expensive proprietary biometric hardware has proven both financially inefficient and technologically inadequate against the scale and sophistication of modern attendance fraud.
The strategic imperative for organizations scaling in the modern economy is the immediate adoption of software-defined biometrics nested securely within a Core Unified Database architecture. By leveraging the advanced computational capabilities, high-resolution optics, and spatial intelligence of standard commodity devices, smartphones and tablets, organizations can deploy sophisticated facial recognition algorithms and precision polygonal GPS geofencing with minimal initial capital expenditure. This technological democratization ensures the absolute, infallible verification of both identity and physical presence, instantly nullifying the financial hemorrhage associated with time theft and unauthorized overtime accumulation.
Platforms such as TimeTrex serve as the definitive benchmark for this architectural evolution. By securely converting complex facial geometry into encrypted digital templates, providing robust offline caching capabilities for distributed environments, and fundamentally unifying the biometric data collection process with the ultimate execution of payroll mathematics, such systems eliminate the inherent fragility and compliance risks of fragmented API networks. The transition to a unified, software-based biometric ecosystem is no longer merely an optimization of human resources administration; it is a fundamental, urgent requirement for securing operational integrity, enforcing strict regulatory compliance, and protecting enterprise capital in an increasingly complex and distributed labor market.
Disclaimer: The content provided on this webpage is for informational purposes only and is not intended to be a substitute for professional advice. While we strive to ensure the accuracy and timeliness of the information presented here, the details may change over time or vary in different jurisdictions. Therefore, we do not guarantee the completeness, reliability, or absolute accuracy of this information. The information on this page should not be used as a basis for making legal, financial, or any other key decisions. We strongly advise consulting with a qualified professional or expert in the relevant field for specific advice, guidance, or services. By using this webpage, you acknowledge that the information is offered “as is” and that we are not liable for any errors, omissions, or inaccuracies in the content, nor for any actions taken based on the information provided. We shall not be held liable for any direct, indirect, incidental, consequential, or punitive damages arising out of your access to, use of, or reliance on any content on this page.
About The Author

Roger Wood
With a Baccalaureate of Science and advanced studies in business, Roger has successfully managed businesses across five continents. His extensive global experience and strategic insights contribute significantly to the success of TimeTrex. His expertise and dedication ensure we deliver top-notch solutions to our clients around the world.
Time To Clock-In
Start your 30-day free trial!
Experience the Ultimate Workforce Solution and Revolutionize Your Business Today
- Eliminate Errors
- Simple & Easy To Use
- Real-time Reporting
Saving businesses time and money through better workforce management since 2003.
Copyright © 2026 TimeTrex. All Rights Reserved.